NextCloud/ownCloud SMB User Authentication Bypass
[CVE-2016-9463]
Vulnerability Details
Disclosure
Rhino Security Labs References
Disclosure Date
03/27/2017
Vulnerability Description
Nextcloud Server before 9.0.54 and 10.0.1 & ownCloud Server before 9.1.2, 9.0.6, and 8.2.9 suffer from SMB User Authentication Bypass. Nextcloud/ownCloud include an optional and not by default enabled SMB authentication component that allows authenticating users against an SMB server.
This backend is implemented in a way that tries to connect to a SMB server and if that succeeded consider the user logged-in. The backend did not properly take into account SMB servers that have any kind of anonymous auth configured. This is the default on SMB servers nowadays and allows an unauthenticated attacker to gain access to an account without valid credentials.
Note: The SMB backend is disabled by default and requires manual configuration in the Nextcloud/ownCloud config file. If you have not configured the SMB backend then you're not affected by this vulnerability.
CVSS Metrics
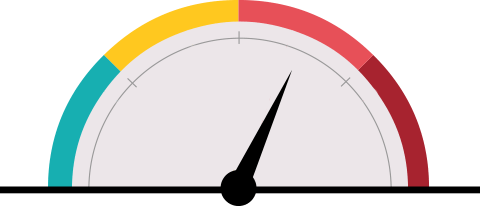
CVSS Rating (version 3.0)
8.1 (High)
Impact Score
Exploitability Score
5.9
2.2
Attack Vector
Network
Attack Complexity (AC)High Privileges Required (PR)None User Interaction (UI)None Scope (S)Unchanged
Confidentiality (C)High Integrity (I)High Availability (A)High
